Configure IAM Tag Permission Policy
After binding cloud resource tags to a CCR enterprise edition, you can use tags to allocate and control access permissions for instances. This document explains how IAM users’ permissions can be controlled using tags to grant different permissions to access various CCR instances.
Background
Tags are a way to categorize cloud resources for better management. IAM can manage user identities and control access permissions for cloud resources based on policies. By combining tags with IAM and using tags as conditions in permission policies, you can achieve more precise permission management for cloud resources.
Operation steps
This step involves using the Baidu AI Cloud root account to create a custom permission policy, UseTagAccessPolicy (which restricts IAM users to accessing only CCR instances with the specified tag test: ccr), and then granting this custom permission policy (UseTagAccessPolicy) to the IAM user.
- Navigate to the Identity and Access Management console.
- Click Policy Management in the left navigation bar to enter the Permission Policy List page.
-
Click Create Policy, and then select Create by Tag in the system pop-up box to enter the Create Permission Policy by Tag page.

-
Complete relevant configurations on the Create Permission Policy by Tag page:
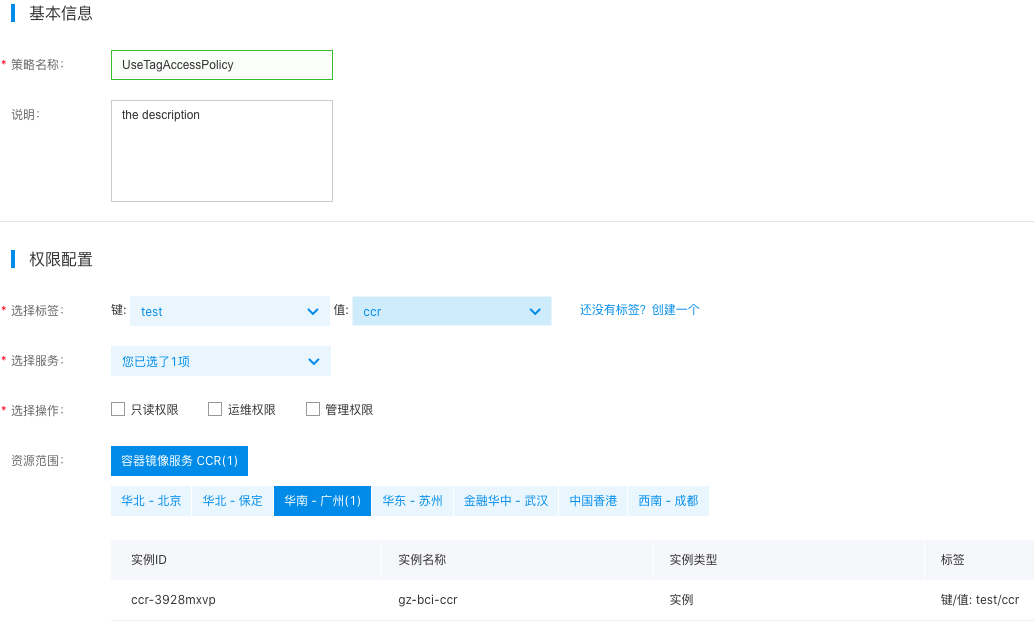
| ConfigMap | Required/Optional | Configuration |
|---|---|---|
| Policy name | Required | Custom policy name: Enter "UseTagAccessPolicy" here. |
| Select tag | Required | Select the tag bound to the target resource; select test: cce here. |
| Select service | Required | Select the cloud service that corresponds to the target resource. Choose "Cloud Container Registry (CCR)" here. The system will automatically filter all CCR instances associated with this tag. |
| Select operation | Required | Specify the IAM user permissions to operate on the target resources. Choose "Read-only Permission" here. Multiple permissions, such as "Operation and Maintenance Permission" and "Management Permission," can also be selected. |
| Resource scope | Required | Indicate the CCR instance for which this policy will apply. The system will automatically match CCR instances from all regions associated with the selected tags. |
1>**Description**
2>
3>* Read-only permission: Have read-only permission for all instances associated with the selected tag.
4>* Operation and maintenance permission: possess the full read-write permissions for all instances associated with the selected tags, excluding instance creation, instance upgrade and renewal
5>* Management permission: possess the full read-write permissions for all instances associated with the selected tags
6>- Click the OK button to complete the creation. You can view the created policy on the Permission Policy List page.
- Grant the custom permission policy to the target IAM user. For specific steps, refer to IAM User Authorization.
